-
【云原生kubernetes系列】--RBAC权限的使用
1.1 API网关
1.1.1 API网关介绍
-
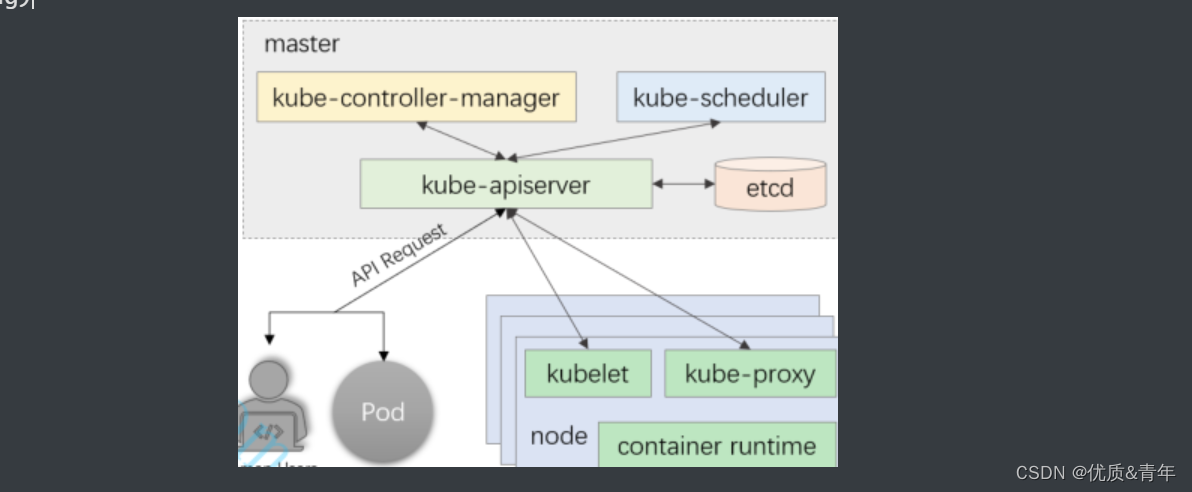
API Server是k8s集群的网关,是能够与etcd通信的唯一入口
-
kube-controller-manager、kube-scheduler、kubelet、kube-proxy,以及后续部署的集群插件CoreDNS、ProjectCalico等,彼此间互不通信,彼此间的所有协作均经由API Server的REST API进行,它们都是API Server的客户端, 确保对API Server的安全访问至关重要。
-
客户端对API Server的访问应经过身份验证以及权限检查
-
为防止中间人攻击,各类客户与API Server间的通信都应使用TLS进行加密,kubelet也会监听一些套接字,提供一个小型的REST API
-
10250是具有所在节点上Pod管理权限的读写端口,应谨慎管理
-
10255仅提供只读操作,是REST API的子集
-
10248是本地healthz端点使用的端口
1.1.2 API网关的访问流程
API Server内置一个三级别的访问控制机制

- 认证:核验请求者身份的合法性
- 授权:核验请求的操作是否获得许可
- 准入控制:检查操作内容是否合规
插件化机制,每种访问控制机制均有一组专用的插件栈
- 认证:身份核验过程遵循 ”或“ 逻辑,且任何一个插件核验成功后都将不再进行后续的插件验证
- 均不成功,则失败,或以“匿名者”身
份访问 - 建议禁用“匿名者”
- 均不成功,则失败,或以“匿名者”身
- 授权:鉴权过程遵循“或”逻辑,且任何一个插件对操作的许可授权后都将不再进行后续的插件验证
- 均未许可,则拒绝请求的操作
- 准入控制:内容合规性检查过程遵循 “与”逻辑,且无论成败,每次的操作请求都要经由所有插件的检验
- 将数据写入etcd前,负责检查内容的有效性,因此仅对“写”操作有效
- 校验和补全(订正)
1.2 RBAC
1.2.1用户分类
- 普通用户(user):被外部或独立服务管理的。管理员分配私钥,常用的kubectl都是普通用户执行的
- 服务账户(ServerAccount):是由k8s API管理的用户,它们绑定到特定的命名空间,并由API服务器自动创建或通过手动通过调用API创建。服务账户与存储为Secrets的一组证书相关联,这些凭据被挂载到pod中,以便进程与k8s API通信(登录dashboard时我们使用的就是SA)。如果是程序需求权限,将Role与ServiceAccount指定(这需要创建ServiceAccount并且在deployment中指定ServiceAccount),是给程序使用的。

11.2.2k8s角色以及角色绑定
1、授权介绍
在RBAC API中,通过以下步骤进行授权:
1、**定义角色:**在定义角色时会指定此角色对于资源的访问控制的规则
2、**绑定角色:**将主体与角色进行绑定,对用户进行访问授权。
角色:
- role:授权特定命名空间的访问权限(对命名空间)
- clusterrole:授权集群的访问权限(对集群)
角色绑定
- RoleBinding:将角色绑定到主体(即subject,其实就是把角色和用户、用户组、服务账户绑定)
- ClusterRoleBinding:将集群角色绑定到主体
主体(subject)
- 用户(user)
- 用户组(group)
- 服务账号(SA)

2、角色介绍(Role和ClusterRole)
Role针对特定的命名空间,ClusterRole针对是整个集群范围内都生效
11.3k8s中kubeconfig的配置以及使用详解
概念:
kubeconfig文件保存了k8s集群的集群、用户、命名空间、认证的信息。kubectl命令使用kubeconfig文件获取集群的信息然后和API Server进行通信
注意:用于配置对集群的访问的文件称为 kubecconfig 文件。也就是说,kubeconfig 文件中包含的内容是集群的配置。但是,并不是必须有个文件名字叫 kubeconfig。默认情况下,kubectl命令从 $HOME/.kube 目录下查找一个名字叫做 config 的文件。可以通过 KUBECONFIG 环境变量或者–kubeconfig 参数来指定其他的 kubeconfig 文件。
kubeconfig中的组成部分:
- Cluster:集群
- user:用户
- context:上下文
kubeconfig支持多集群、多用户、多认证
实际使用场景:
- kubelet使用证书认证(kubelet和api server进行认证)
- 用户使用token进行认证
- 管理员为不同的用户提过不同的证书
都可以使用kubeconfig来组织集群、用户、命名空间的信息。同样也可以使用context在集群和命名空间之间进行切换
11.3实验
11.3.1 允许用户访问指定的Namespace下的资源
要求:
- 创建用户wengsq
- 允许用户wengsq操作Namespace linux下所有的pod和deployment
1、创建用户
root@k8s-master1:/app/yaml/rbac# kubectl create sa wengsq -n linux- 1
2、创建角色
root@k8s-master1:/app/yaml/rbac# cat wengsq-role.yaml apiVersion: rbac.authorization.k8s.io/v1 kind: Role metadata: name: wengsq-role namespace: linux rules: - apiGroups: - "" resources: - pods - pods/exec verbs: ["*"] - apiGroups: - apps resources: - deployments verbs: ["*"] root@k8s-master1:/app/yaml/rbac# kubectl apply -f wengsq-role.yaml #验证 root@k8s-master1:/app/yaml/rbac# kubectl get role -n linux NAME CREATED AT wengsq-role 2024-02-23T06:36:53Z root@k8s-master1:/app/yaml/rbac# kubectl describe role wengsq-role -n linux Name: wengsq-role Labels: <none> Annotations: <none> PolicyRule: Resources Non-Resource URLs Resource Names Verbs --------- ----------------- -------------- ----- pods/exec [] [] [*] pods [] [] [*] deployments.apps [] [] [*]- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
3、将用户与角色绑定
新建一个名为role-bind-wengsq的Rolebinding
root@k8s-master1:/app/yaml/rbac# cat role-bind-wengsq.yaml apiVersion: rbac.authorization.k8s.io/v1 kind: RoleBinding metadata: name: role-bind-wengsq namespace: linux roleRef: apiGroup: rbac.authorization.k8s.io kind: Role name: wengsq-role subjects: - kind: ServiceAccount name: wengsq namespace: linux root@k8s-master1:/app/yaml/rbac#kubectl apply -f role-bind-wengsq.yaml #验证 root@k8s-master1:/app/yaml/rbac# kubectl describe rolebindings.rbac.authorization.k8s.io role-bind-wengsq -n linux Name: role-bind-wengsq Labels: <none> Annotations: <none> Role: Kind: Role Name: wengsq-role Subjects: Kind Name Namespace ---- ---- --------- ServiceAccount wengsq linux- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
4、使用wengsq账号的token登录dashboard并验证(1.24版本以前的sa的secret是自动生成,1.24以后要手动生成)
root@k8s-master1:/app/yaml/rbac# kubectl get secrets -n linux NAME TYPE DATA AGE default-token-b55qx kubernetes.io/service-account-token 3 2d22h wengsq-token-jmfx5 kubernetes.io/service-account-token 3 26h root@k8s-master1:/app/yaml/rbac# kubectl describe secrets wengsq-token-jmfx5 -n linux Name: wengsq-token-jmfx5 Namespace: linux Labels: <none> Annotations: kubernetes.io/service-account.name: wengsq kubernetes.io/service-account.uid: 9c74cff9-351e-4f8e-8414-192cceb1d9d9 Type: kubernetes.io/service-account-token Data ==== token: eyJhbGciOiJSUzI1NiIsImtpZCI6IjNKazJfUnF2c0stSkFVbHZkT2VPVXRRSlBINVM5SEtmWTRqR013RmpKRUkifQ.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJsaW51eCIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VjcmV0Lm5hbWUiOiJ3ZW5nc3EtdG9rZW4tam1meDUiLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlcnZpY2UtYWNjb3VudC5uYW1lIjoid2VuZ3NxIiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZXJ2aWNlLWFjY291bnQudWlkIjoiOWM3NGNmZjktMzUxZS00ZjhlLTg0MTQtMTkyY2NlYjFkOWQ5Iiwic3ViIjoic3lzdGVtOnNlcnZpY2VhY2NvdW50OmxpbnV4OndlbmdzcSJ9.NkUN9E6wYcjw4TzFA5julmOOkey2Gq1jUOUw6jP5f9Z7lb9MnbG3ecZ58-RqZ7GL7TD4BsbCQAYd_uAiZseHOvdb8wYmPIZZF-T04MnjwX_O2ZVTCm3pN-w2p0nAsFe8ofPxWjFWM5NvJBwhXHvBl8roh0bz5X-Fg8NELRv7vsO0xd5TkVQFBiVOn5n_0rWvdjXhwgNGjG6VSEGI9WUXPB1kw-wLcLZ39ZclCA1hJLHSt5NCLASnYRZC83J_OAnSnOwE6woCQyRLXHzcZYfYIC2gxsdQEoC1K-S97IliJ0qwmnGijRUN_CKsVCQI0uKX1FFJpWnvIes0EHMsbZivfw ca.crt: 1350 bytes namespace: 5 bytes- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18


11.3.2 生成普通用户config文件
1.编写证书配置文件
root@k8s-master1:/app/yaml/rbac# cat wengsq-csr.json { "hosts": [], "key": { "algo": "rsa", "size": 2048 }, "names": [ { "C": "CN", "ST": "NanJing", "L": "Nanjing", "O": "Pana", "OU": "System" } ] }- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
2.签发证书
签发成功会生成:wengsq-key.pem、wengsq.csr、 wengsq.pem三个文件
root@k8s-master1:/app/yaml/rbac# ln -sf /etc/kubeasz/bin/cfssl* /usr/bin/ root@k8s-master1:/app/yaml/rbac# cfssl gencert -ca=/etc/kubernetes/ssl/ca.pem -ca-key=/etc/kubernetes/ssl/ca-key.pem -config=/etc/kubeasz/clusters/k8s-01/ssl/ca-config.json -profile=kubernetes wengsq-csr.json |cfssljson -bare wengsq 2024/02/23 16:20:26 [INFO] generate received request 2024/02/23 16:20:26 [INFO] received CSR 2024/02/23 16:20:26 [INFO] generating key: rsa-2048 2024/02/23 16:20:27 [INFO] encoded CSR 2024/02/23 16:20:27 [INFO] signed certificate with serial number 654959555428526687192265662714543254530197189889 2024/02/23 16:20:27 [WARNING] This certificate lacks a "hosts" field. This makes it unsuitable for websites. For more information see the Baseline Requirements for the Issuance and Management of Publicly-Trusted Certificates, v.1.1.6, from the CA/Browser Forum (https://cabforum.org); specifically, section 10.2.3 ("Information Requirements") root@k8s-master1:/app/yaml/rbac# ll total 60 drwxr-xr-x 2 root root 299 Feb 23 14:59 ./ drwxr-xr-x 11 root root 136 Feb 21 10:48 ../ -rw-r--r-- 1 root root 260 Feb 20 17:39 role-bind-wengsq.yaml -rw-r--r-- 1 root root 80 Feb 21 17:16 sa.yaml -rw-r--r-- 1 root root 555 Feb 22 13:43 tomcat-app1.yaml -rw-r--r-- 1 root root 202 Feb 21 17:04 wengsq-csr.json -rw------- 1 root root 1675 Feb 21 17:04 wengsq-key.pem -rw-r--r-- 1 root root 271 Feb 23 14:59 wengsq-role.yaml -rw-r--r-- 1 root root 972 Feb 21 17:04 wengsq.csr -rw------- 1 root root 6215 Feb 21 17:06 wengsq.kubeconfig -rw-r--r-- 1 root root 1363 Feb 21 17:04 wengsq.pem- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
3.生成普通用户的kubeconfig文件
1、生成普通用户kubeconfig文件 root@k8s-master1:/app/yaml/rbac# kubectl config set-cluster cluster1 --certificate-authority=/etc/kubernetes/ssl/ca.pem --embed-certs --server=https://172.17.1.101:6443 --kubeconfig=wengsq.kubeconfig Cluster "cluster1" set. 2、将证书信息嵌入kubeconfig文件 root@k8s-master1:/app/yaml/rbac# kubectl config set-credentials wengsq --client-certificate=/app/yaml/rbac/wengsq.pem --client-key=/app/yaml/rbac/wengsq-key.pem --embed-certs=true --kubeconfig=wengsq.kubeconfig User "wengsq" set. 3、设置上下文参数 root@k8s-master1:/app/yaml/rbac# kubectl config set-context cluster1 --cluster=cluster1 --user=wengsq --namespace=linux --kubeconfig=wengsq.kubeconfig Context "cluster1" created. 4、设置默认上下文 kubectl config use-context cluster1 --kubeconfig=wengsq.kubeconfig 注意:如果查看没有wengsq.kubeconfig文件,配置一下环境变量export KUBECONFIG=~/.kube/wengsq.kubeconfig- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
4、将wengsq 账号的secret 的token写到wengsq.kubeconfig这个文件


-
-
相关阅读:
Javassist-ConstPool常量池
嵌入式软件常用测试工具
算法 数据结构 递归冒泡算法 java冒泡算法 优化递归冒泡 数据结构(九)
小米面试——案例总结
【CCF】第30次csp认证——202305-1重复局面
『第十一章』数据持久化:CoreData 与 CloudKit
【优化器】BGD、SGD、MSGD、Momentum、Adagrad、RMSPprop、Adam
独家首发,阿里内部纯手码spring boot项目,你学会了吗?
[附源码]java毕业设计龙虎时代健身房管理系统
alexnet pytorch模型和onnx模型速度对比
- 原文地址:https://blog.csdn.net/weixin_58519482/article/details/136259523
